Do you want to know how to bypass firewalls? This is not a good idea. However, here are some of the best methods to help you bypass the firewall when you are desperate.
Before going deeper, you must understand that bypassing a firewall in school or anywhere is risky. Today, it is often employees, and school students find it hard to access some websites. The reason is that some organizations and institutions use networks to blacklist specific websites which they do not want anyone to access through their ISPs.
Such networks that filter websites and contents rely on firewalls while accessing restricted websites. We know you are wondering what a firewall is and how they work as well as how to bypass them. By the end of this article, you will have learned everything you ought to know.
Therefore, before going into details about bypassing a firewall, it is also good to know what a firewall is. Hence firewall is simply a network security software or hardware and sometimes a combination that monitors outgoing and incoming network traffic. Thus, the firewall can deny or accept a request for specific traffic.
We have broken down our article into sections for easy understanding. Let us now go through various methods and step by step guide on bypassing a firewall. We will also discuss some of the possible consequences at the end so that you weigh and decide. let us dive into various methods.
[lwptoc]Efficient Ways to Bypass Firewall
1. By Using Free Web Proxy Sites

An efficient way to bypass firewalls is through t free web proxy site. If you want to try out this method, then follow our guide as shown below:
Step 1: Launch your browser. That is, double-click your preferred browser on your computer.
Step 2: Then go to your selected proxy site, and as such, they might include HideMe, ProxyFree, or CroxyProxy. Sometimes, you might realize that your network has blocked all the above free web proxies, and so in this case, search free online proxy in the search box and get other relevant free website proxy sites.
Step 3: Then once you are there, go to the search bar and then click on it. You will be able to see the website or URL text bot found in the middle of the search bar box.
Step 4: Enter the website addresses you are restricted or blocked to access into that text box. Some website proxies do not support searching a website using the keyword on their search bars.
Step 5: Immediately you are done typing in or searching, then click enter. The proxy will now load your search results to open the restricted website. It might take longer to display the results since web proxies do not utilize a direct path to request from the computer to the server.
So, when you follow the above steps correctly and sue the tab on the proxy, you will be able to see any restricted website. But remember to say within the proxy when you want to open a new browser window and tab. When you try going outside, it will fail to load the content.
2. Use the Smartphone As a Mobile Hotspot

Another efficient method to bypass firewalls is using smartphones as hotspot devices. But, first thing first, the procedure is very vital. Here we go:
Step 1: The step is making sure that the smartphone or carrier allows tethering. This is the ability of your computer to allow the use of cellular data as a WIFI network connection. Not all allow tethering. The best way is to call the carrier and ensure that your device allows it.
Step 2: Then turn wifi on your smartphone. If it is an iPhone, navigate to the settings, click wifi, and click the green switch again to turn on wifi. For the case of Android, from the top of your screen-swipe downward and then long-press the wifi icon.
Step 3: Then using a USB cable, connect your smartphone to the computer. Using the 3.0 side of your smartphone charge, plug it into the USB port on your computer. a situation may also arise when using a Mac desktop. In this case, you must have a USB 3.0 to USB-C adapter to connect your smartphone to the computer through the cable.
Step 4: Then also, plug the other end of the cable into your smartphone; be it an iPhone or Android gadget, it would be able to connect.
Step 5: Then next, enable hotspot tethering on your mobile gadget. The procedure varies depending on the kind of smartphone you are using. On iPhone, go to the settings, click personal hotspot and click on the white switch personal hotspot to enable tethering.
While on Android, again swipe downward starting from the top of your screen and then click the settings button, click more, and from the menu below wireless and networks, click tethering and portable hotspot and finish the process by toggling the USB tethering button.
Step 6: After that, you should select a smartphone as your network connection. most computers prioritizes phone network connection once connected to the ethernet standing. If it is not the case with your computer, there are two scenarios here: windows and mac. Click on the wifi icon, then select the phone name using a mac, but when you are using windows, it connects without even asking your password since you are using the cable.
After that, you can launch your browser and surf any website unrestricted. The computer is connected to the cellular connection instead of the internet, meaning you are using the current location. This way, you will be able to bypass geo-restrictions. However, it would be best if you were informed that browsing through hotspots tethers consumers to more cellular data. This means you should be prepared to incur extra charges on your budget if you want to download large files.
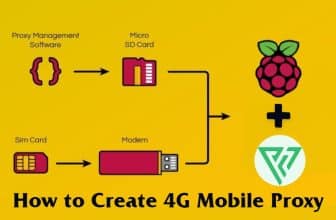
3. By Using a Proxy

A firewall is something unique, and to this extent, you understand its functionality, and when it has your name on it, you become a target person to get a block. You can also track it using third-party tools and access information or unblock restricted websites. Proxy is another option to help you bypass firewalls. Therefore, follow these guides to do it using your smartphone:
Step 1: The first thing is to ensure that you are connected to the available network. Therefore, connect your phone to wifi or turn on your cellular data and proceed.
Step 2: Make sure that your proxy settings are in position. Ensure that the proxy username, password, and IP addresses are on standby at your fingertips. When using windows or instead network, set the proxy network and settings, and for this case, we mainly use mobile phones.
Step 3: Then navigate to the settings on your phone, click and scroll to network and internet.
Step 4: Tap on the mobile network button. some mobile phones do not have this option. Therefore, if you find a cellular network, still use this and proceed.
Step 5: While on a mobile or cellular network, make sure that you turn on your mobile. When using Android, tap on advanced options; while on iOS, click on the mobile option.
Step 6: The tap on APN( Acces Point Name) choice on the phone
Step 7: Then, while in the APN section, find the proxy server icon, type in the IP addresses, and enter the port number. Afterward, you will be able to browse freely and access any site blocked by firewalls.
You can even learn more about setting up a proxy using the computer.
4. By Using a VPN

Next on our list of effective ways to bypass firewalls is VPNs. They work like proxies, but they are much faster and more secure. There are different VPNs online, but the procedure for using them remains the same. Here is the step by step guide you need to follow:
Step 1: Choose a VPN of your choice first. There are countless VPNs ( Virtual Private networks) that are available online. You can select popular ones such as NordVPN, ExpressVPN, etc. select either that fits your needs. Refer to the previous article for more efficient VPNs.
However, there are exceptions where VPN cannot work. Such cases include the school library, computer library, or workplaces. This is because you must change computer settings in this situation to utilize VPN. But, a VPN you select will mask your IP address while you browse. Most online VPNs offer free services, but you must pay a discounted fee to access advanced services.
Step 2: After selecting, choose a subscription to your VPN. You must create an account to get your password, server address, username, and other relevant information.
Step 3: Then open your device's VPN settings. The guideline varies depending on the device you are using. For instance, the Windows desktop will open the start menu, click Settings, tap network, and internet, click on the VPN button and finalize by clicking add VPN connection, which is found at the top of your page.
With mac, use the Apple menu icon, then system preference, tap on the network and + button located at the lower-left corner, then tap interface a drop-down box. On Android, click the settings icon, click more, and click VPN an option below wireless and network, then click +to add VPN. Lastly, you will click settings> general on the iPhone devices, then tap VPN> add VPN configuration.
Step 4: It is time to enter the VPN details, and also, this step procedure varies based on the type of VPN you have selected.
Step 5: Then save the configurations of your VPN immediately after you enter the information. When using windows, you will access the save button at the bottom of the page. Wich mac, tap create, enter all the configurations, then hit apply, and on iPhone, you will find the option ‘done found at the top right corner of your screen. Then Android is like windows-click save.
Step 6: Now connect the VPN. On the window desktop, choose the VPN from the page and tap the connect button below it to add any needed information. The same procedure applies to mac. However, when using iPhone, you will have to go to the white switch and click on the right, then type in any information you will be prompted. Lastly, on Android, navigate to the VPN section, click connect and include any needed details.
You are done, and you can now enjoy browsing without firewall restrictions.
5. By Using Tor

Tor is just a website browser like chrome and firefox. The operation is the same. However, you can browse using this browser anonymously. This browser uses the three layers of proxies: the entry node, middle relay & exit node. This means that for one to find your real location or IP address, they must be able to trace three different proxies, which sounds almost impossible. HSo, how does that happen in bypassing firewalls?
Step 1: Using your usual browser, launch it and visit Tor website and download the software.
Step 2: Ensure that you download the correct version with your most preferred language
Step 3: Double click so that the system extracts the file page and confirms that the files downloaded are all you need.
Step 4: Install the software to your device and launch it. Click on the tor icon/shortcut on the desktop or start the browser icon. It will redirect you to the torn network within a few minutes.
Step 5: Then get the restricted firewall site that you wish to unblock, then copy its URL
Step 6: Change to the tor page and verify that there is a connection. one way to know that the connection is working is through green wording, which indicates that the connection is successful. When you have a red icon, the connection has failed.
Step 7: If connected, paste your copied URL on the search box of tor and click the enter button. And in the long run, when the browser accesses the content on the restricted site, then tor would have been bypassed the firewall. We also recommend using a tor bridge in cases where the ISP has blocked the tor connection. Yes, the tor network will be visible, but the bridge will tend to relay the network absent within the tor directory, making it hard to track.
6. By Using Ultrasurf

Ultrasurf also offers you another reliable way to bypass firewalls. This is the procedure:-
Step 1: First, you must grasp the concept of Ultrasurf. This tool does not require installation; thus, you can even use it with heavily restricted desktops. So, when you open Ultrasurf, it automatically connects to the available proxies and then uses any default browser to launch an incognito window. You can then use the browser to surf firewall-restricted sites. But remember, this service is only compatible with Windows, Mac, Android, and Chrome extensions.
Step 2: Secondly, you now have to visit the Ultrasurf website using your browser on a computer. If it becomes hard operating on a restricted computer, download it through the home page, store it in a flash drive, and run it from the flash.
Step 3: Download the software by clicking the download icon, a blue icon located in the upper left corner of your page. It will be downloaded as a zip file.
Step 4: Then extra the files from the zip folder. Point and double-tap the zipped folder, tap extract, then hit extract all and click extract again.
Step 5: Click and open Ultrasurf, double click on the icon you extracted and begin to run it. Be patient until the default browser opens.
Step 6: After that, you can now start browsing without any restrictions. Use the default browser to visit any website without issues.
7. Access Your PC Remotely

Also, accessing your pc remotely helps you bypass the firewall. Most importantly, you need third-party server software to help you access the home desktop through another computer. You can bypass any firewall restrictions when you suspect that someone is blocking your access to a website and, again, your regular access through this method.
8. Use IP Addresses Instead of Website Names

lastly, you can bypass the restrictions of a website by using the IP address of the website instead of the name. You must be aware that any name of a website you search on the internet has its IP address to which it is converted while sending a request to the server. This is because the computer does not know names, and that is why they must first convert using DNS( domain name server).
This phenomenon is related to situations where a firewall uses a domain to look at or block a site instead of the IP addresses. This implies that when you visit a site using the IP address, the firewall will not be able to track you, thus giving you freedom of access. It is hard to find the IP address of a website. There is a platform you can use to search the IP addresses. That is, whatIsMyIPaddress.
Warning for Bypass Firewall

There are many negative consequences of breaking any rules, such as firing, expelling, or even suspension. The worst-case scenario can be stealing your details and even catching malware spreading over your device. Firewalls are only meant to keep your online privacy and security. And at school, they are intended to help promote learning while enhancing productivity at work. Therefore, before you decide to bypass the firewall, learn about the negative workarounds and risks:-
1. Steal Your Details

When using a proxy to bypass a firewall restriction, remember that all details go through the server before routing to the destination. Still, the server host keeps and traces the traffic you are after. And so, it is good to be patient until you arrive home. Free things are not for free because developers use your details and sell them to the marketers to curate ads. Therefore, you should be keen.
2. It Can Affect Your Desktop with the Virus

interns of privacy, free services are not safe. They are most prone to malware and online services since the developers intend to make money through advertisements. They do not care what people are advertising, and in case of this case, it becomes easy for your computer getting the deadly virus that can even spread to the whole workplace or school.
3. Expel or Suspension

the Institutions have a strict policy on computer usage, so they manage what you do on computers. So, when you circumvent the policy, you are likely to undergo the consequences. Such rules are like banning a specific website, and when you are caught bypassing firewalls, you might be expelled or suspected from the school or workplace. This is not good for your future hustle.
4. Facing Legal Action

Remember that bypassing firewalls is an illegal activity. Therefore, it is not advisable to access unlawful content or websites. The consequence of accessing or using illegal content is worse. If it is a school, they might pass you to the next level of authority, which means you need to face legal ramifications.
Therefore very, never bypass the firewall and avoid it at all costs unless necessary. In the first place, you are aware of why one can decide to use a firewall, and you should respect the decision. Otherwise, firewalls are essential in protecting your device from malware and hackers' attack while online.
Conclusion
We hope this article was resourceful if you plan to bypass the firewall. We have provided various methods to efficiently unblock any restricted website or content and guide you on step-by-step procedures.
Before using them, ensure that the proxy and VPNs keep you anonymous. Otherwise, the consequences are worse than any convincing reason. Therefore, unless necessary, avoid bypassing firewalls to evade losing your personal information, facing laws, or infecting your computer with deadly viruses.